Application Load Balancer
Select your Load Balancer Plan
- All the load balancer plans are listed based on different memory, vCPU, storage configuration, and price.
- Select a plan to create the new load balancer.
Type
- After selecting the plan, choose the Application Load Balancer type.
Details
- Name: A default name is provided based on the selected plan, but you can modify it.
- Type: Select either Internal or External, depending on your requirement.
Frontend protocol
Choose Frontend Protocol: It checks for connection requests using a specified protocol and port for front-end (client to load balancer) connections. E2E Networks Load Balancer supports the following protocols:
- HTTP and HTTPS protocols independently.
- HTTPS (secure HTTP) using SSL/TCL: Supports the X-Forwarded headers and requires an SSL certificate on the load balancer.
- HTTP: Supports the X-Forwarded headers.
HTTP Redirect
Select "Redirect HTTP to HTTPS" if you use HTTPS for the front-end protocol of the load balancer. For web user safety, accessibility, or PCI compliance, it may be essential to enable this redirect.
Target Mapping
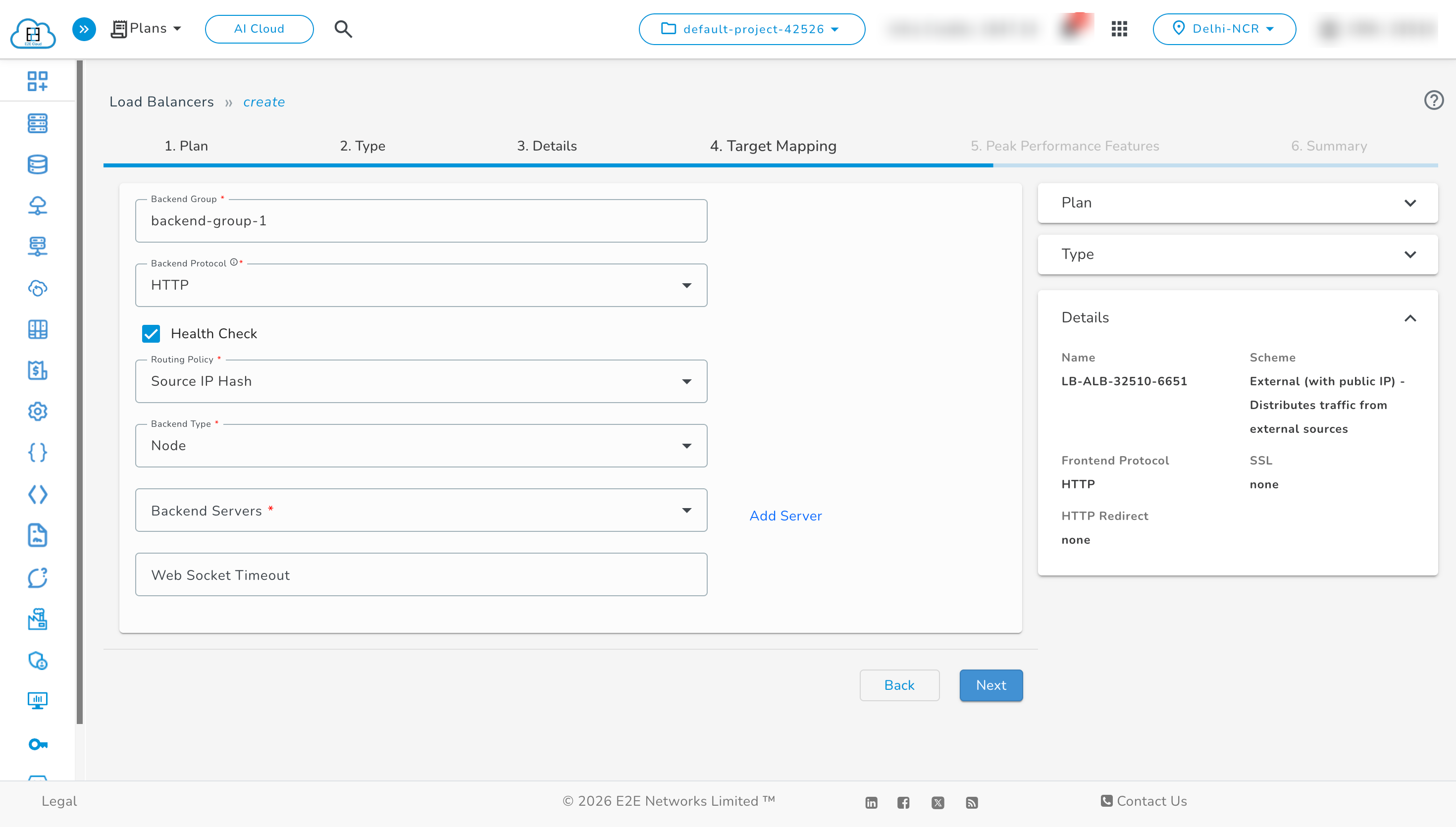
Backend Group : A Backend Group is a logical set of backend servers that receive traffic from the load balancer. It defines the destination pool for requests and applies health checks and routing policies to ensure traffic is sent only to healthy backends.
Backend Protocol : The Backend Protocol specifies how the load balancer communicates with backend servers.
It determines whether traffic is forwarded using HTTP or HTTPS. For HTTPS backends, SSL certificates can be self-signed or issued by an internal CA authority, enabling TLS termination or end-to-end encryption.
Health Check
Your load balancer checks the health of the web application configuration you specify. If the backend node responds with a 2xx or 3xx HTTP status code for the defined URL path, it is marked as UP; otherwise, it is marked as DOWN.
- Select "Add HTTP Health Checks" to define HTTP-based monitoring for the health of your backend nodes.
- Define a URL path to which HTTP HEAD requests will be sent to fetch the response code.
Note: The default URL path is
/, which can be changed to any other URI path as required.
Routing Policy
Choose Balancing Policy: Different load balancing policies offer different benefits:
- Round Robin: Distributes connection requests evenly among backend servers.
- Source IP Hash: Routes based on a hash of the source IP to keep a user on the same backend server.
- Least Connection: Distributes traffic by sending requests to the server with the least active connections.
Backend Type
In the List Type, select either Node or Auto Scale Group (for auto-scaling group nodes) to configure the backend connection.
Node
Registering an E2E node adds it to your load balancer. The load balancer monitors the health of registered nodes and routes requests only to healthy nodes.
- Select Node in the list type field to display the Node Details section.
- Specify the details of virtual nodes you wish to register behind the load balancer, including name, IP (preferably private IP if on E2E cloud), and port.
Add Servers
Click on Add Servers to add a backend server in the backend group.
- After adding backend servers, view the backend servers list by clicking the dropdown.
You can also set a websocket timeout for an ALB.
Auto Scale Group
Registering your Auto Scaling group with a load balancer helps you set up a load-balanced application because EAS enables you to dynamically scale compute nodes based on varying workloads and defined policy. This feature allows you to meet seasonal or fluctuating infrastructure demands, optimize cost, and distribute incoming traffic across your healthy E2E nodes—enhancing scalability and availability.
- Select the Dynamic Scale group in the list type field. The node details section will display.
- In the Scale Group Details section, select an application scaling group from the dropdown list to register behind the Load Balancer.
- After selecting the scale group, define the port to send/receive traffic via the Load Balancer in the Target Port field.
To add an auto-scaling group, click on Add New.
Peak Performance Features
Create New VPC - Enable this option to use a VPC IP as the default VPC IP for your load balancer, allowing internal connections.
- After creating a VPC, it will appear in the dropdown list.
- There are two types of VPCs available:
Default VPC: Provided by E2E with a pre-defined CIDR.
Custom VPC: User-created, where you can also optionally select an associated subnet.
- Add New Reserve IP - Enable this option to use a reserved IP as the default Public IP for your load balancer. You can dynamically update backend resources without downtime by re-assigning the reserved IP address.
- After creating the IP, it will appear in the dropdown list.
BitNinja
BitNinja is a server security tool that combines powerful defense mechanisms. Each protected load balancer learns from every attack, applying this information across all BitNinja-enabled servers and load balancers. Learn more.
Enable BitNinja - Enable this option to use BitNinja for your load balancer. BitNinja offers various modules to defend against cyberattacks, is easy to install, requires minimal maintenance, and provides immediate protection.
Timeouts
Configure different timeout values like connection timeout, client timeout, server timeout, and HTTP keep-alive timeout as needed.
Encryption
Encryption in Load Balancer ensures that all incoming and outgoing traffic between clients and backend nodes is securely transmitted over encrypted channels. When HTTPS/SSL is enabled, the Load Balancer terminates SSL at its endpoint, decrypts the incoming request, and forwards the traffic to the backend servers. This prevents data interception, protects sensitive information, and guarantees secure communication over the public network.
Security Group
A Security Group attached to a Load Balancer acts as a virtual firewall that manages both inbound and outbound traffic. It ensures that only permitted IP ranges, networks, and protocols are allowed to communicate with the Load Balancer and its backend nodes. When a Load Balancer is created, a default Security Group is automatically selected and applied. Users also have the flexibility to create a new Security Group or can select from the previously created security group, during the Load Balancer creation process and assign it immediately. Additionally, the newly created Security Group can be set as the default for future Load Balancers. This allows users to enforce custom access rules, improve security, and maintain tighter control over network communication.
- Inbound rules determine what type of traffic is allowed to reach the Load Balancer (e.g., HTTP/HTTPS from specific networks or public access).
- Outbound rules control what traffic the Load Balancer can send out, including allowed IP ranges, ports, and network destinations.
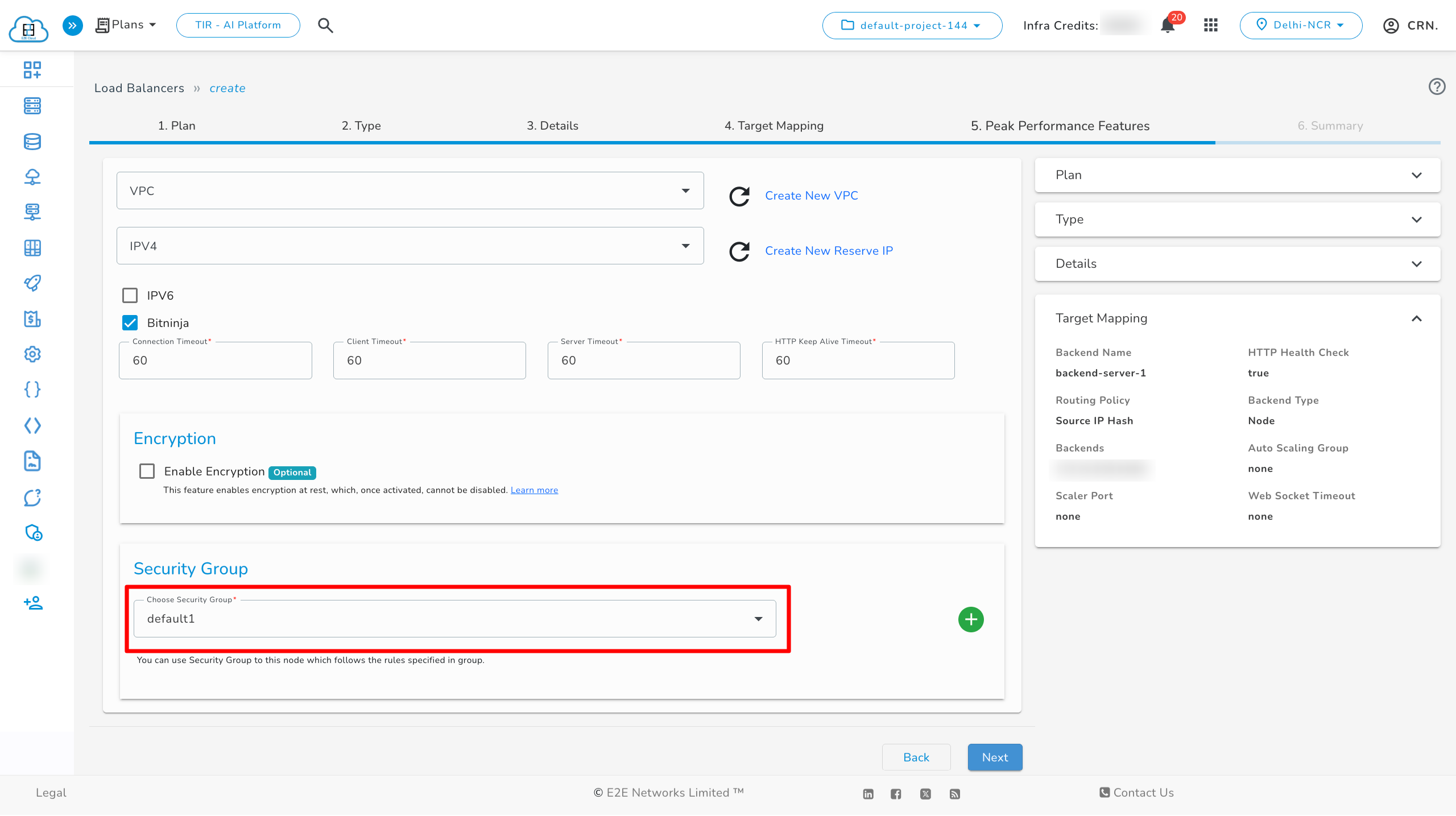
Configure a Security Group for Load Balancer
-
Click the “+” icon to create a new Security Group.
-
Enter a name for the Security Group. Adding a description is optional.You may also choose to set this Security Group as the default.
-
Define the required Inbound and Outbound rules based on your access needs.Click Create to finish.
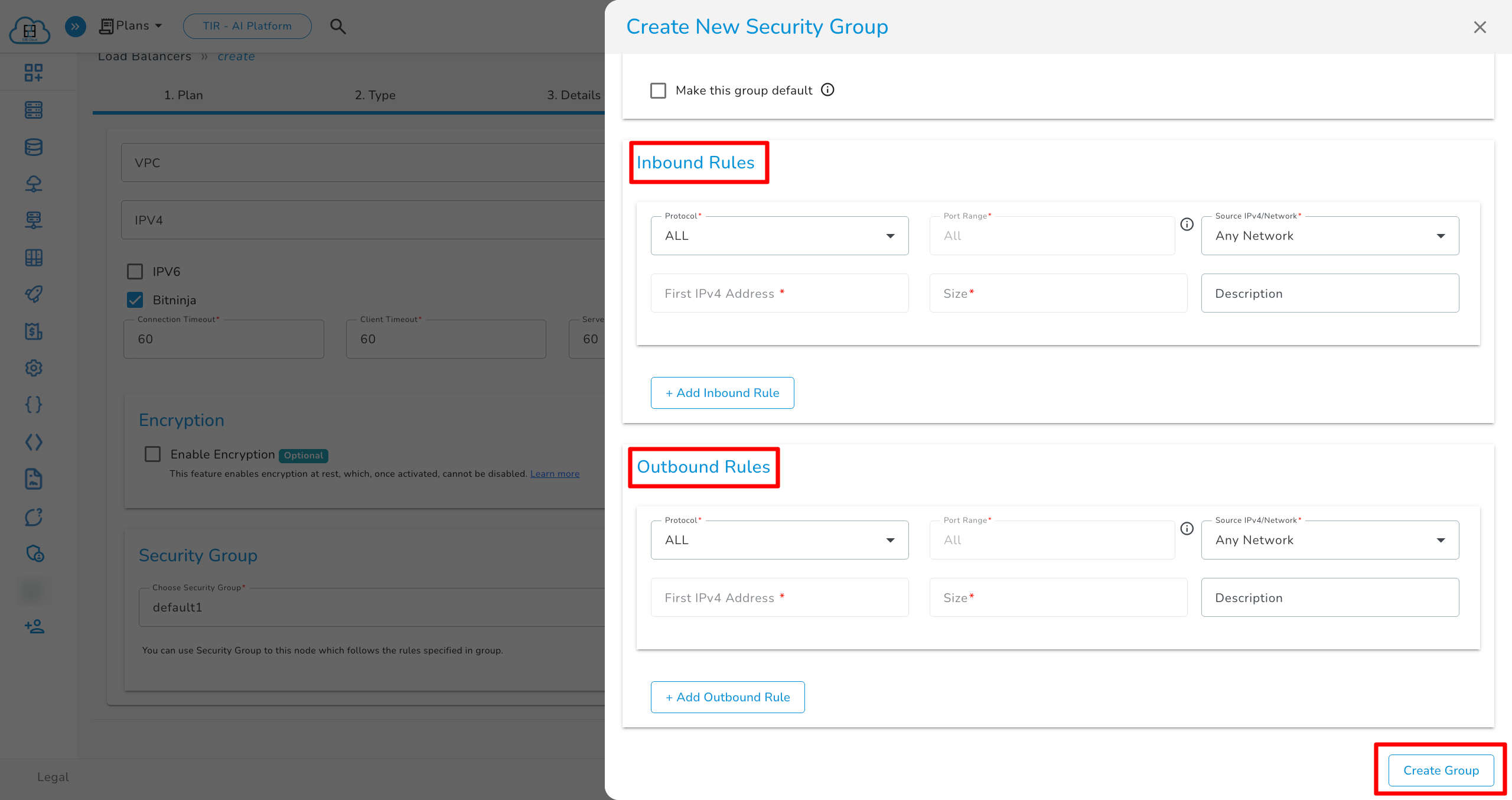
After the Security Group is created, it will appear in the list of available groups. You can then select it from the Security Group dropdown menu while creating or updating your Load Balancer.
Summary
In the Summary section, verify your Plan, Type, Details, Network Mapping, and Peak Performance Features.
Deploy Load Balancer
After completing all fields, click Submit. The setup may take a few minutes, after which you will be redirected to the ‘Load Balancers’ page.
Application Load Balancer Info
You can review basic, security, backend configurations, and network details of your load balancer on the Load Balancer Info tab.
Network
In the Network section you can review the following details for the Load Balancer:
Public IP — the public IP address assigned to the Load Balancer.
IPv6 — IPv6 address (if provisioned).
Associated VPC — the Virtual Private Cloud (VPC) networks attached to the Load Balancer.
Add a new VPC
-
Use this to attach an existing VPC to the Load Balancer.
-
In the Network section, click the + button (Add VPC) located near the VPC list or toolbar.
-
A drawer or modal will open showing available VPCs (or a form to create/select one).
-
Select the VPC you want to attach. If necessary, configure any additional options presented (subnet selection optinally) and Click Attach VPC confirm.
Note: Wait for the UI to show the VPC in the Associated VPC list—this indicates the VPC is successfully attached.
Detach (remove) a VPC
Detach a VPC when you want to remove network connectivity between the Load Balancer and that VPC.
- Choose Detach (or Remove) from the action list.
- Confirm the action in the confirmation dialog.
-
The VPC will be removed from the Associated VPC list and will no longer show under the Network section.
-
It will be detached and removed from the network section.
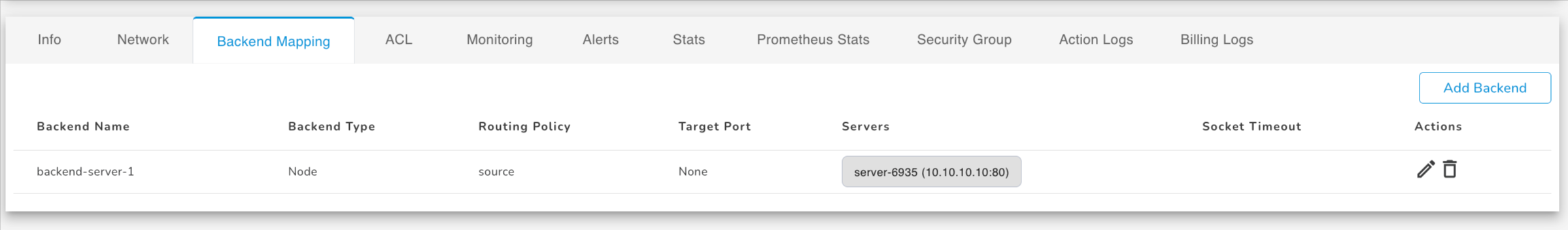
Backend Mapping
Once your load balancer is created, you can access and manage it from the My Account Portal. Click on the installed LoadBalancer instance to see various management options.
To add a backend, click on Add Backend.
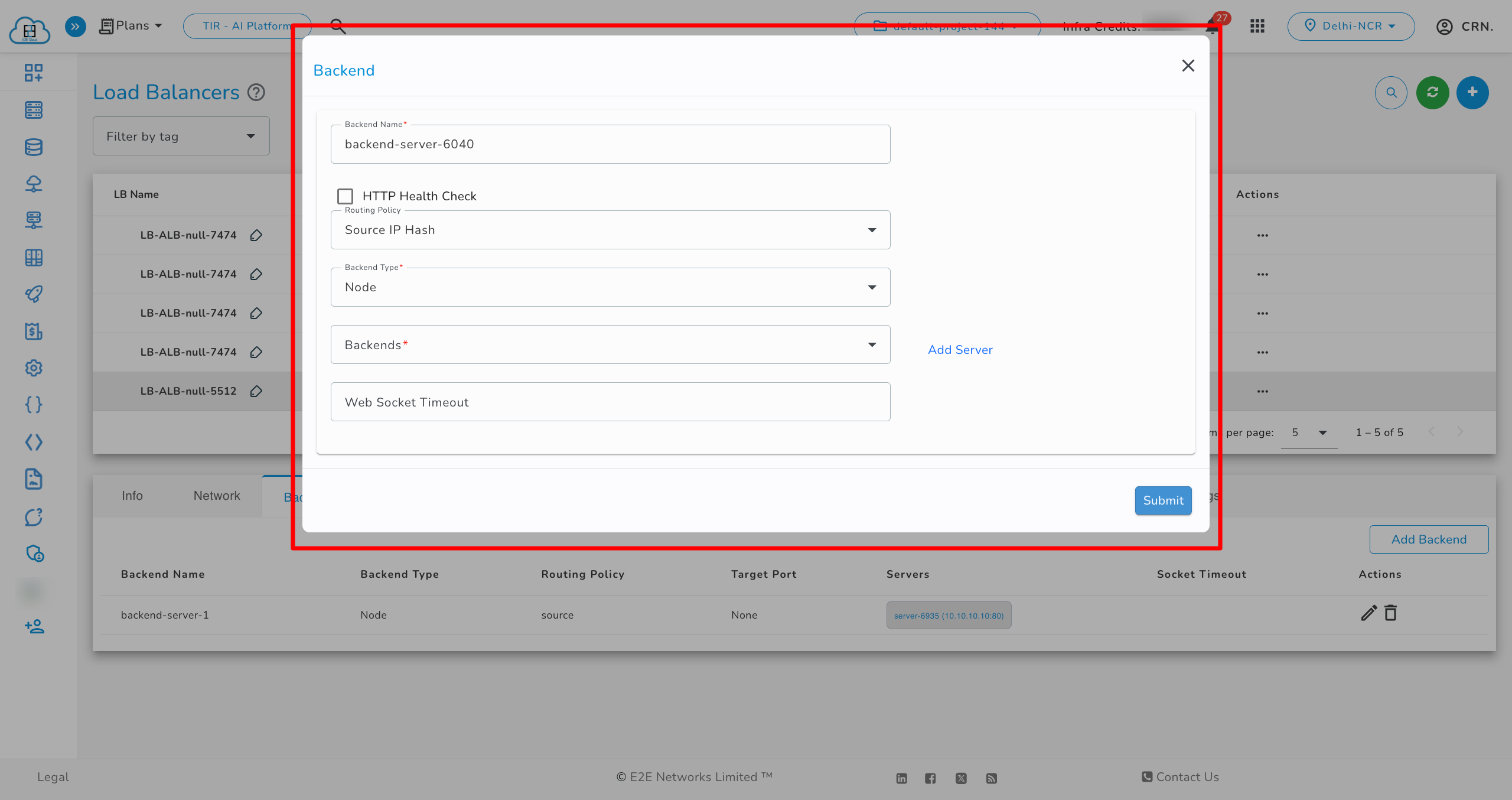
After adding a backend, it will appear in the list below.
Users can add or edit multiple backends simultaneously. After making edits, a “Save and Deploy” button appears along with an info icon. Click on Save and Deploy to save changes.
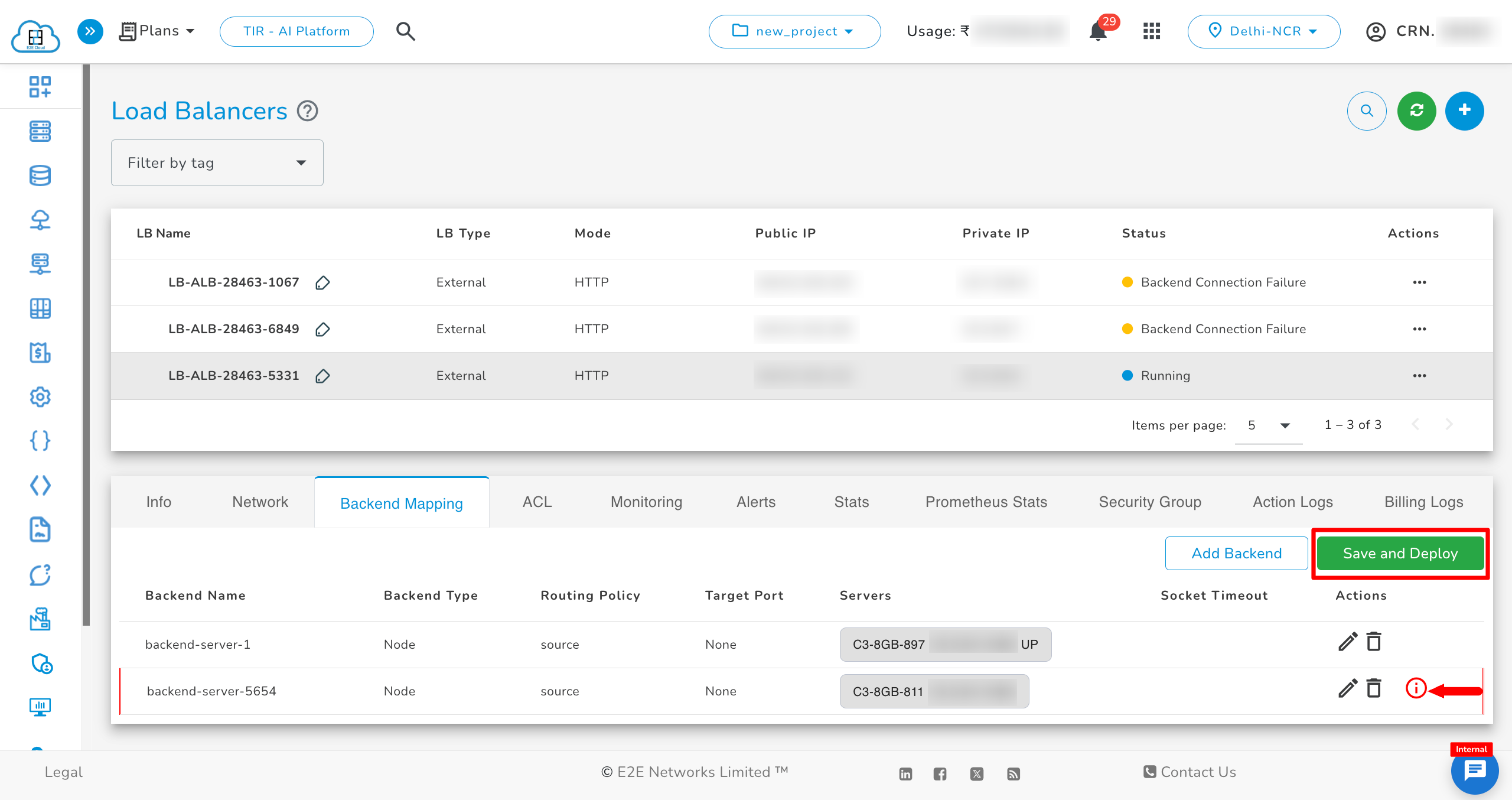
- The Edit Load Balancer page allows you to modify backend and frontend configurations.
- You can delete backend and frontend configurations from the Delete Load Balancer page.
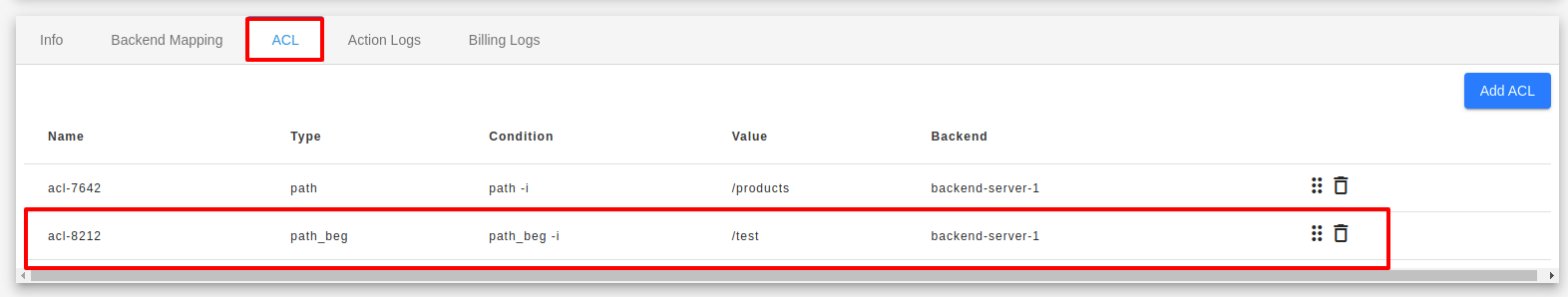
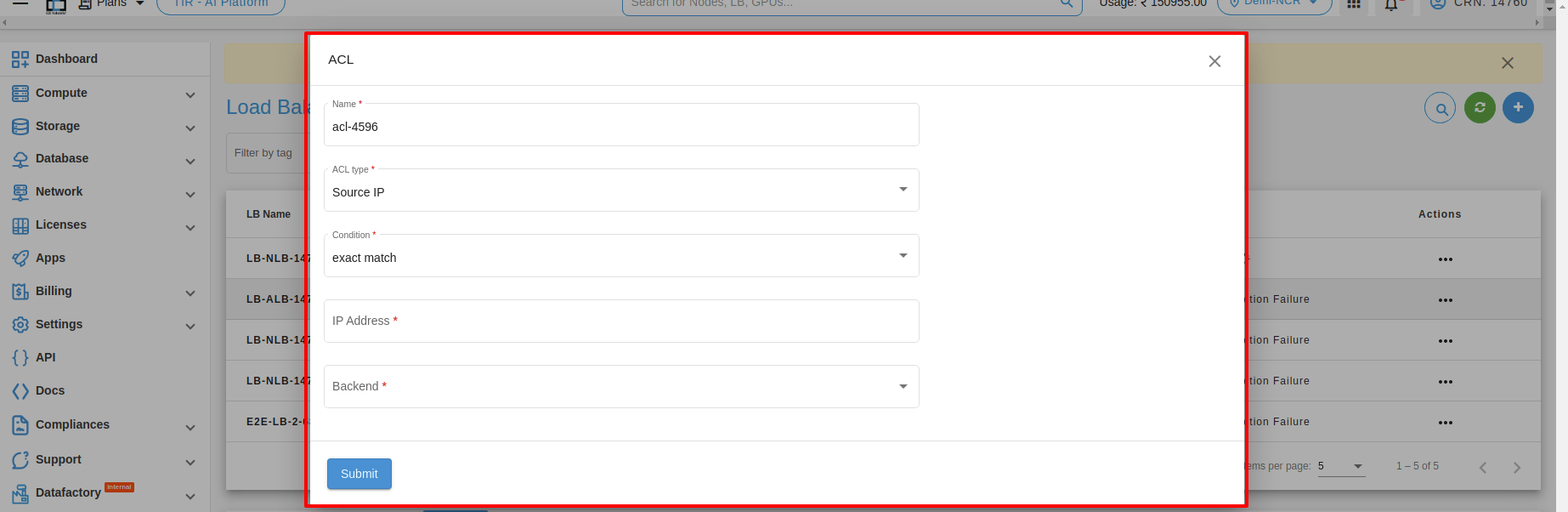
ACL
You can add ACL by clicking ADD ACL button under the ACL tab.
Users have the option to add multiple ACL rules simultaneously. After making desired edits, a “Save and Deploy” button will appear. Additionally, an info icon will be displayed next to the newly added rules. Click on the “Save and Deploy” button to save your changes.
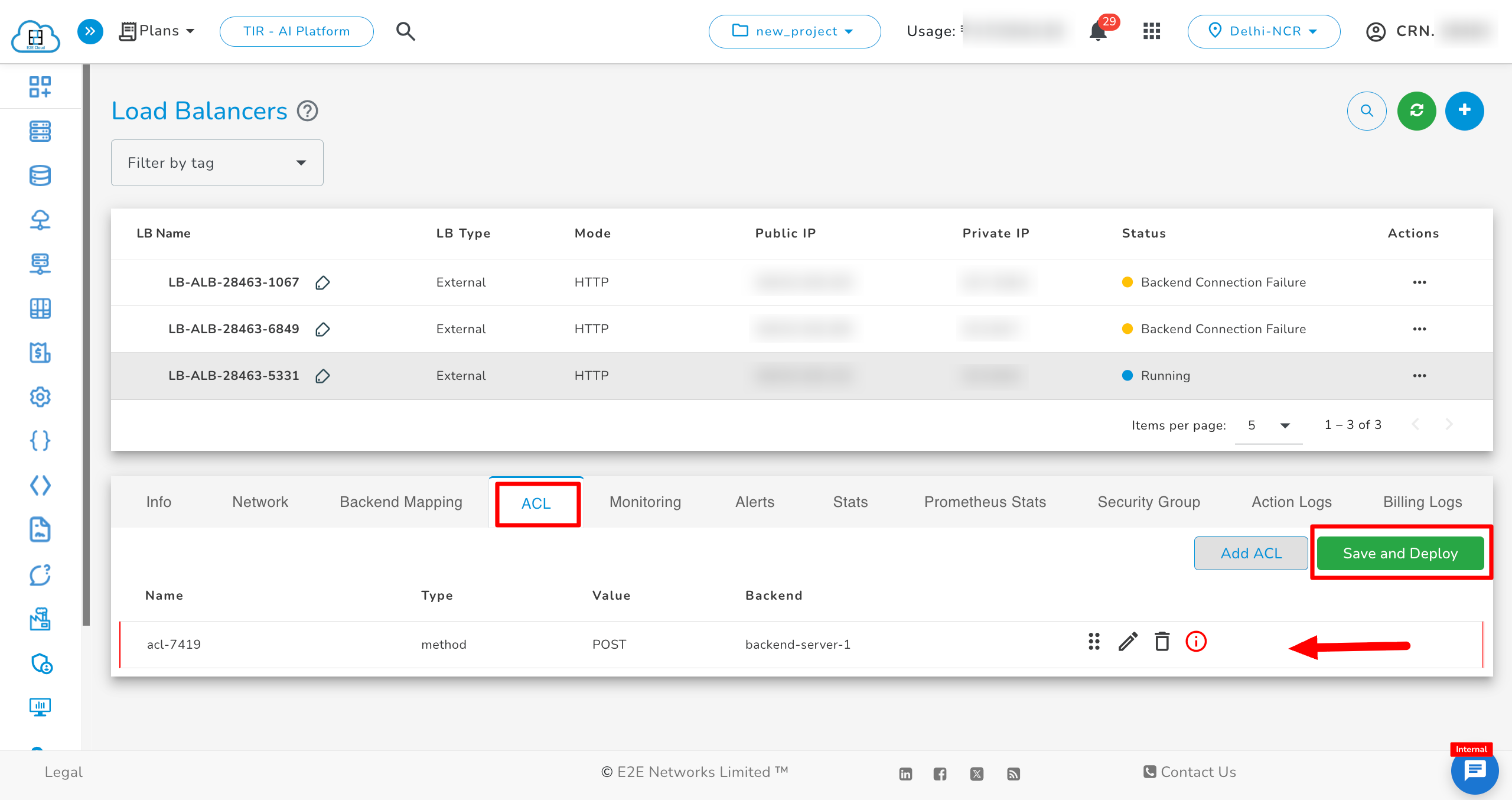
Access rules can be added based on five conditions.
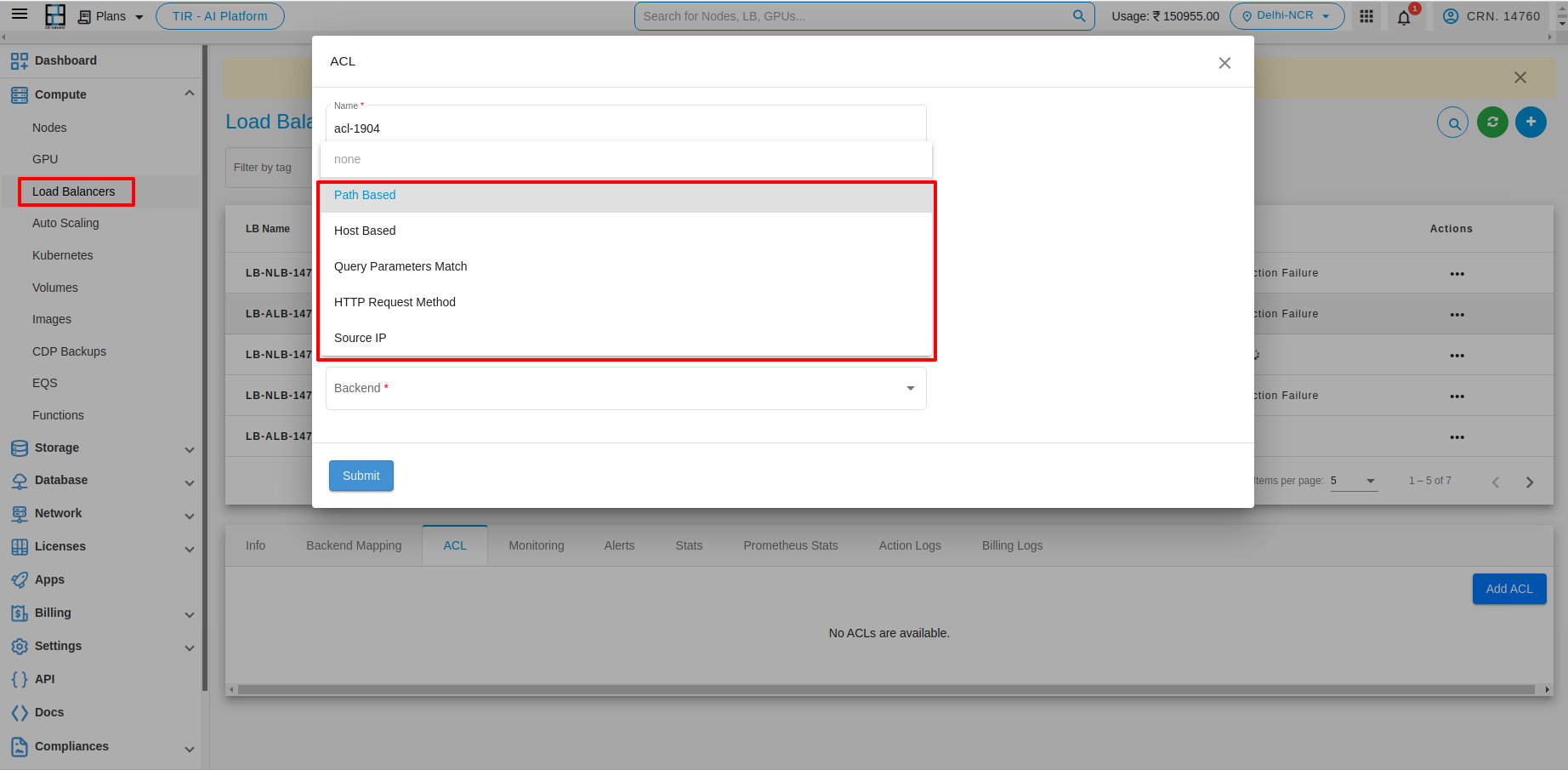
- Path Based Condition
- Host Based Condition
- Query Parameters Match
- HTTP Request Method
- Source IP
1. Path Based Condition
You can use path conditions to define rules that route requests based on the URL in the request. The path pattern is applied only to the path of the URL, not to its query parameters. For example, in the below image the path is added as e2enetworks.com/test.
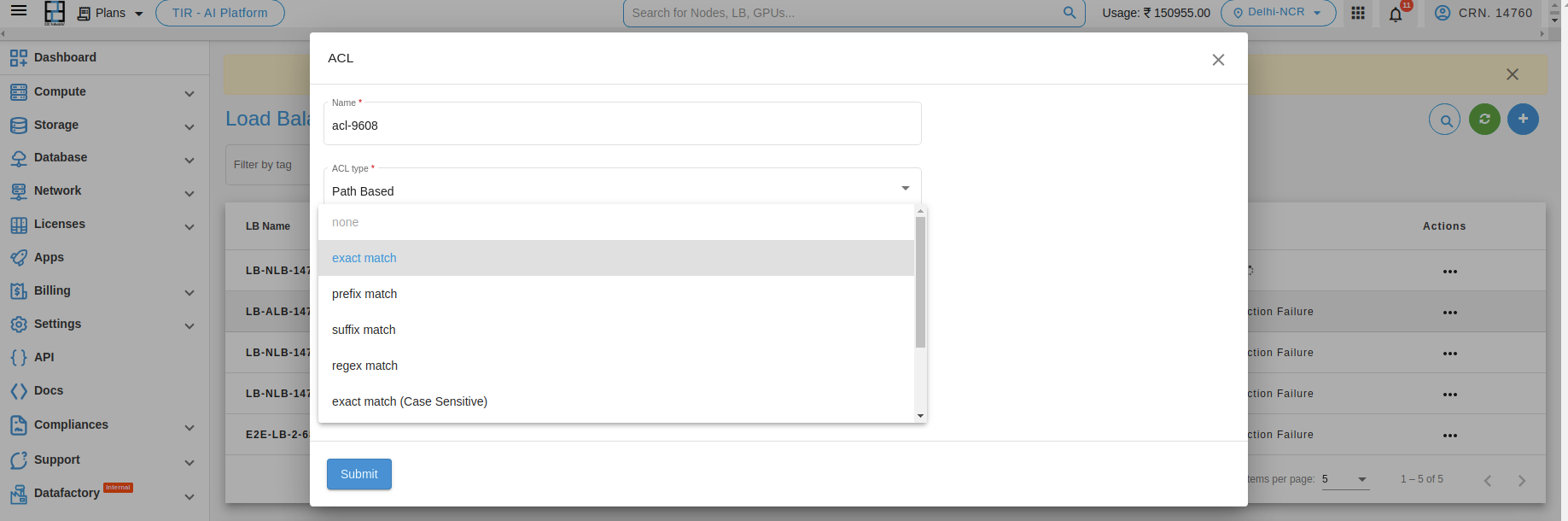
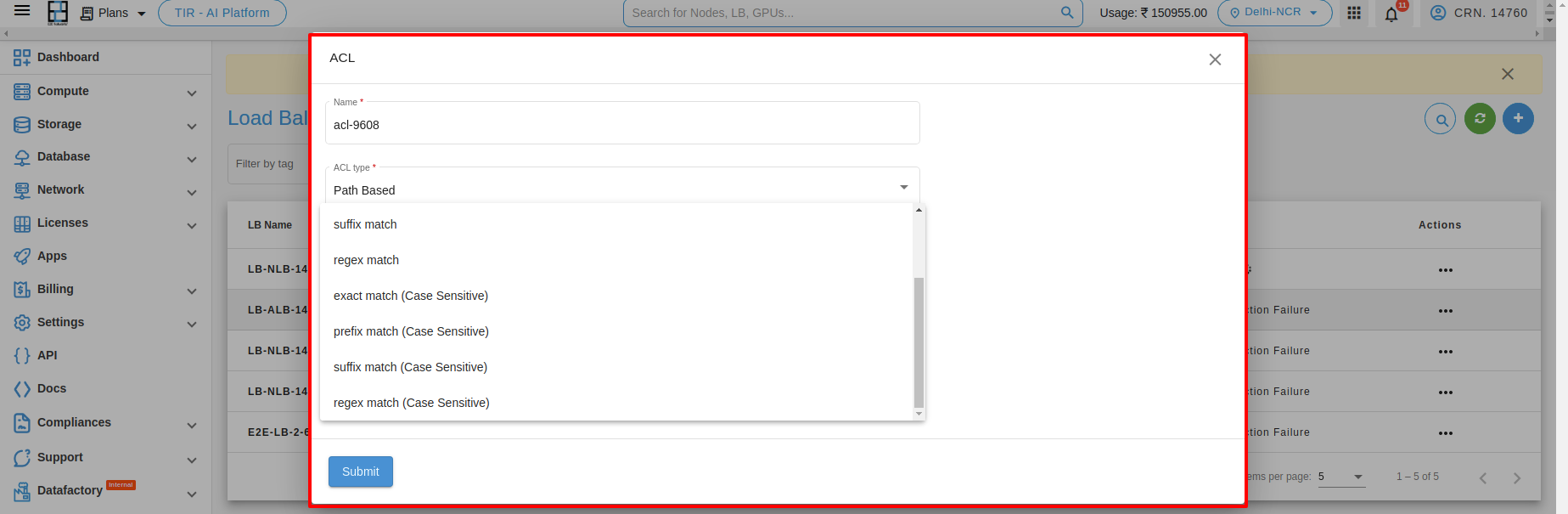
Path Matching Types
-
Exact Match: Matches exactly "pathbase".
Example: "pathbase" -
Prefix Match: Matches any word beginning with "pathbase".
Example: "pathbasefolder", "pathbaseconfig", "pathbasedirectory" -
Suffix Match: Matches any word ending with "pathbase".
Example: "datapathbase", "sourcepathbase", "projectpathbase" -
Regex Match: Matches any word containing "pathbase".
Example:\b\w*pathbase\w*\b(matches words like "pathbasefile", "mypathbaseproject", etc.) -
Exact Match (Case Sensitive): Matches "pathbase" exactly with the same capitalization.
Example: "pathbase" (matches), "PathBase" (does not match) -
Prefix Match (Case Sensitive): Matches any word beginning with "pathbase" with exact capitalization.
Example: "pathbaseFolder" (matches), "PathBaseConfig" (does not match) -
Suffix Match (Case Sensitive): Matches the suffix "pathbase" with exact capitalization.
Example: "pathbase" (matches), "PathBase" (does not match) -
Regex Match (Case Sensitive): Matches words containing "pathbase" with exact capitalization.
Example:\b\w*pathbase\w*\b(matches "pathbasefile" but not "mypathbaseProject")
After adding the ACL type Path Based and conditions, you can see the list below.
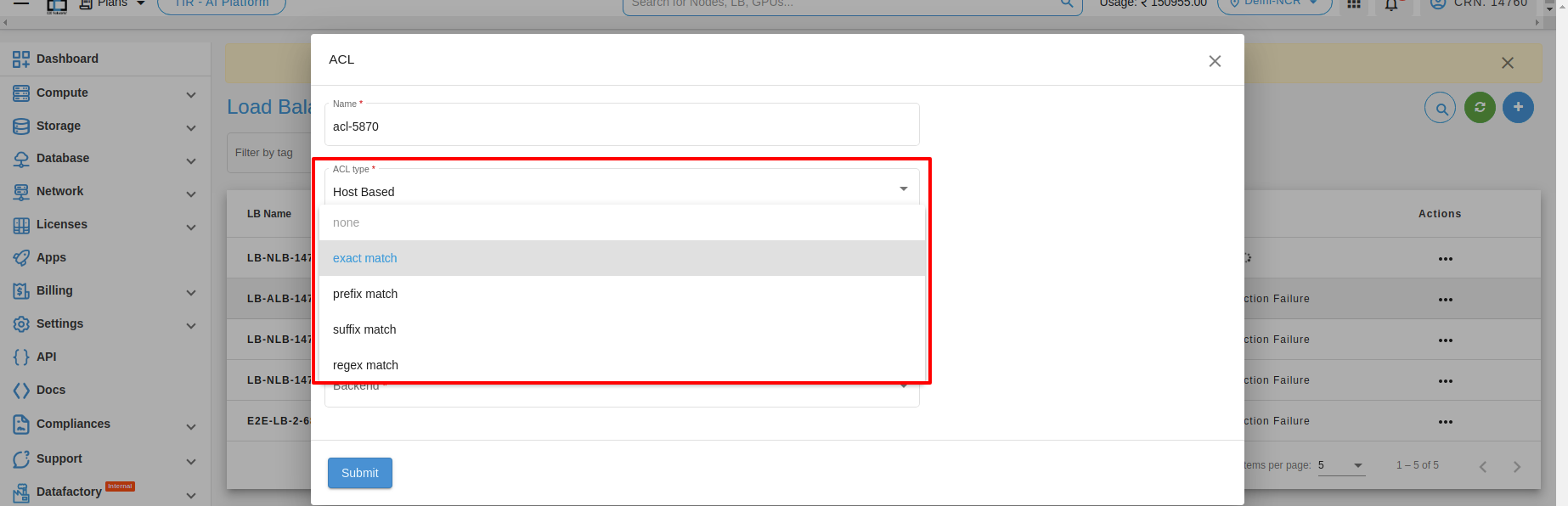
2. Host Based Condition
Use host conditions to define rules that route requests based on the hostname in the host header, known as host-based routing. For example, the host is added as test.e2enetworks.com.
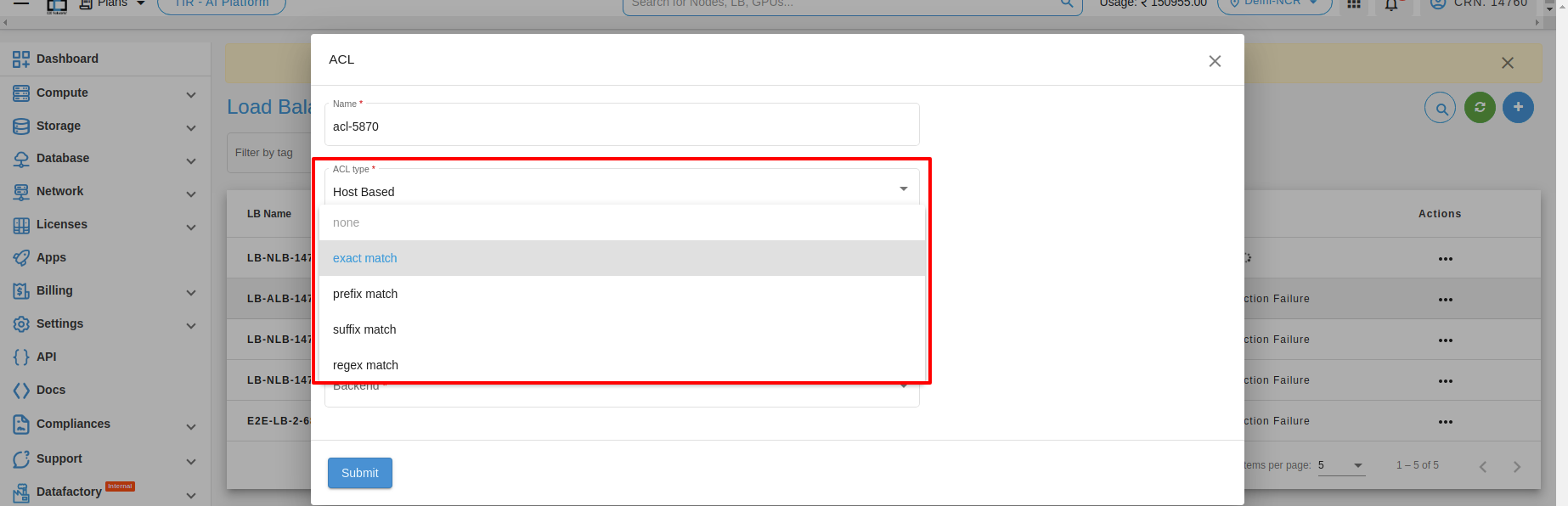
Host Matching Types
-
Exact Match: Matches exactly "hostbase".
Example: "hostbase" -
Prefix Match: Matches words beginning with "hostbase".
Example: "hostname", "hosting" -
Suffix Match: Matches words ending with "hostbase".
Example: "database", "homebase" -
Regex Match: Matches any word containing "hostbase".
Example:\b\w*pathbase\w*\b
After adding the ACL type Host Based and conditions, you can see the list below.
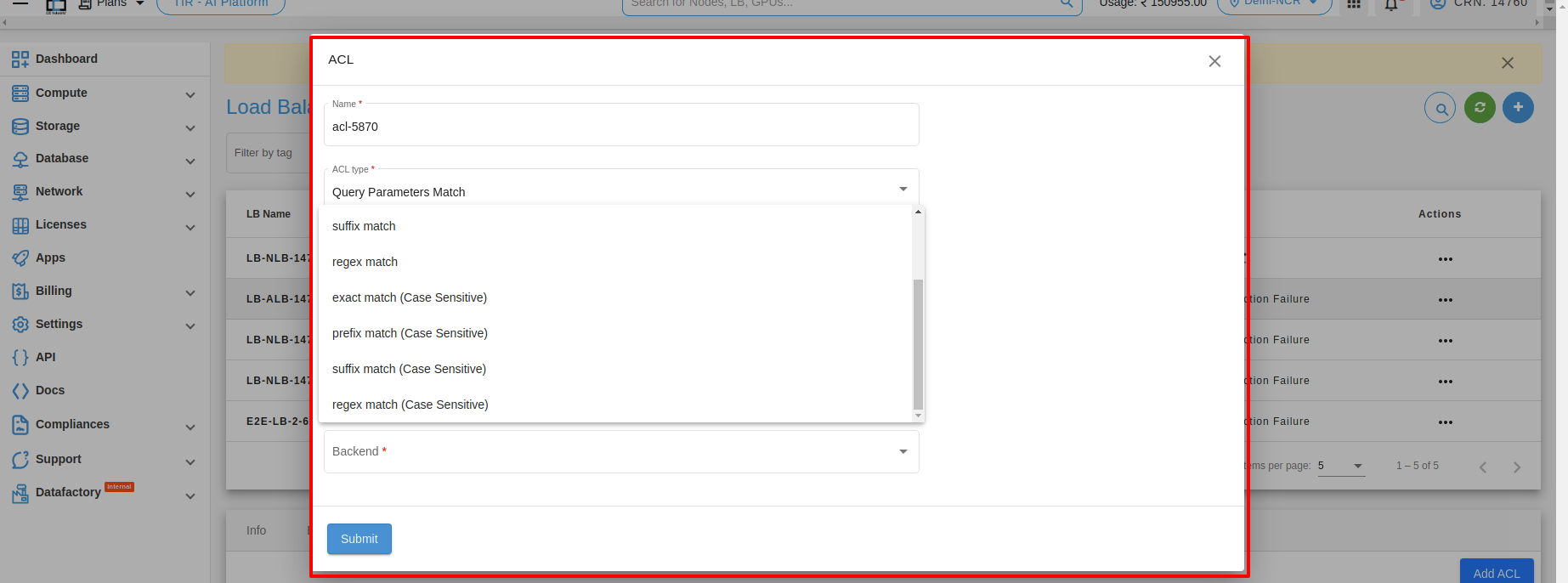
3. Query Parameters Match
Query parameters are used to pass data from a client to a server through the URL. Matching options include exact match, prefix match, suffix match, and regex match.
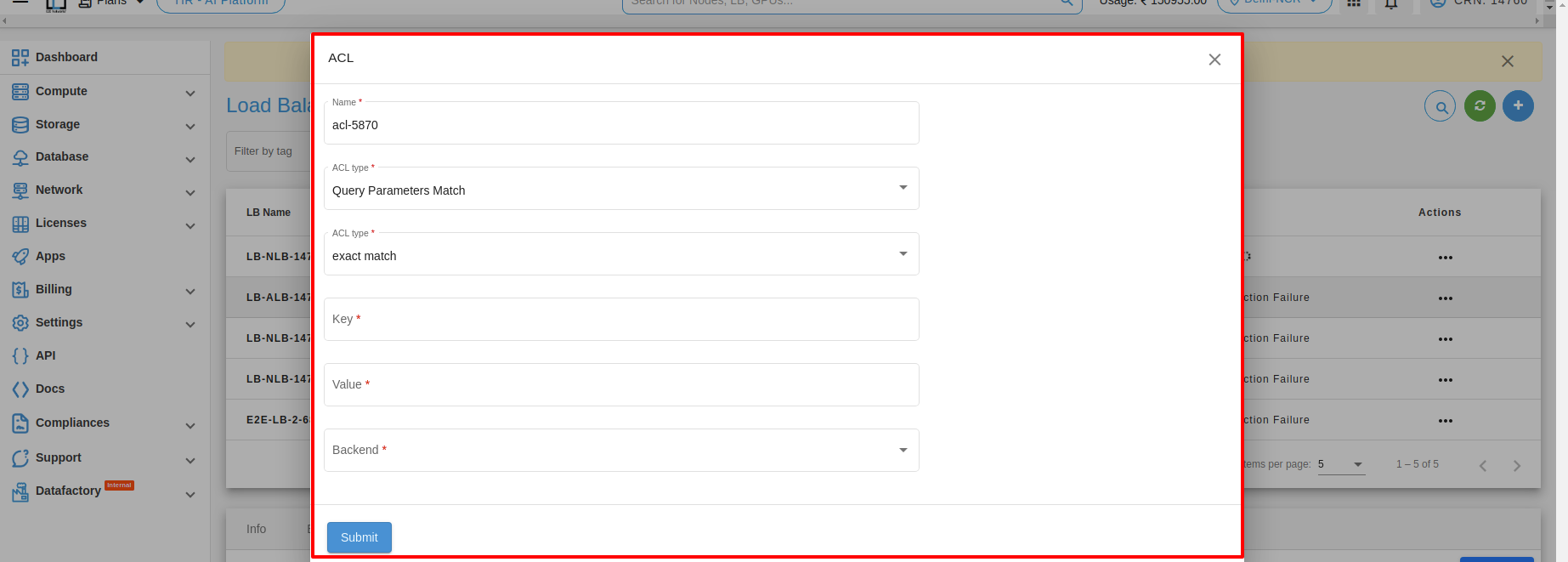
Query Parameter Matching Types
-
Exact Match: Matches specific values exactly.
Example:https://example.com/users?id=123 -
Prefix Match: Matches values that start with a specific string.
Example:https://example.com/search?query=phone -
Suffix Match: Matches values that end with a specific string.
Example:https://example.com/files?type=pdf -
Regex Match: Matches values based on complex patterns.
Example:https://example.com/articles?search=python\+\+programming -
Exact Match (Case-Sensitive): Matches specific values exactly with case sensitivity.
Example:https://example.com/users?id=USER123 -
Prefix Match (Case-Sensitive): Matches case-sensitive values starting with a specific string.
Example:https://example.com/search?query=phone -
Suffix Match (Case-Sensitive): Matches case-sensitive values ending with a specific string.
Example:https://example.com/files?type=PDF -
Regex Match (Case-Sensitive): Matches case-sensitive patterns using regular expressions.
Example:https://example.com/articles?search=Python\+\+Programming
4. HTTP Request Method
HTTP request method matching is used to direct incoming requests to specific servers or services based on the HTTP method used in the request.
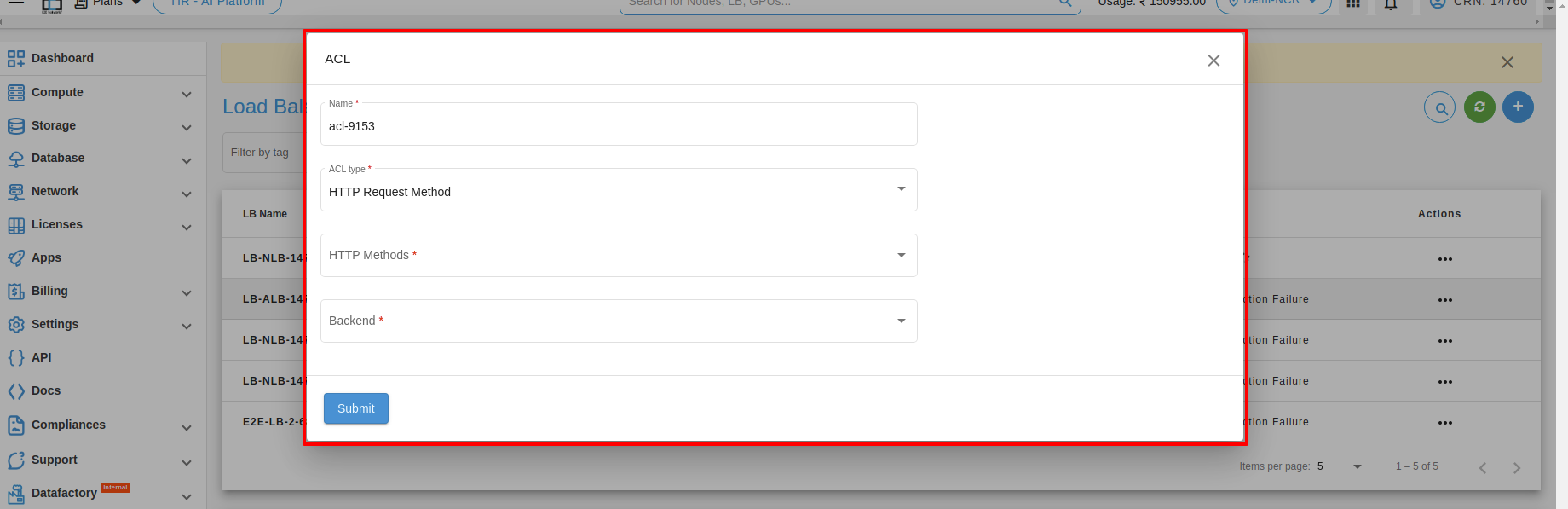
-
Match GET Requests: Routes all GET requests to a specific server for static content.
-
Match POST Requests: Routes all POST requests to a server for handling form submissions.
-
Match PUT Requests: Routes all PUT requests to a server for file uploads.
5. Source IP
Source IP matching is a feature commonly used in load balancers to direct incoming requests to specific servers or services based on the source IP address of the request. Here's an example of how source IP matching can be used in a load balancer.
-
Match requests from a specific IP address: This type of source IP matching is used to direct all incoming requests from a specific IP address to a specific server or service. For example, if you have a client that is accessing your application from a dedicated IP address, you could use a load balancer to match all incoming requests from that IP address and direct them to a specific server.
-
Match requests from a range of IP addresses: This type of source IP matching is used to direct all incoming requests from a range of IP addresses to a specific server or service. For example, if you have a set of servers that are optimized for handling requests from a specific geographic region, you could use a load balancer to match all incoming requests from that region and direct them to those servers. Here's an example configuration in the load balancer:
Monitoring
Monitoring is an important part of maintaining the reliability, availability, and performance of your load balancer. You can check the monitoring information for your load balancer on the Monitoring tab. This information is collected from your load balancer and processes raw data into readable graphs. Each graph is based on one of the different metrics. Learn more.
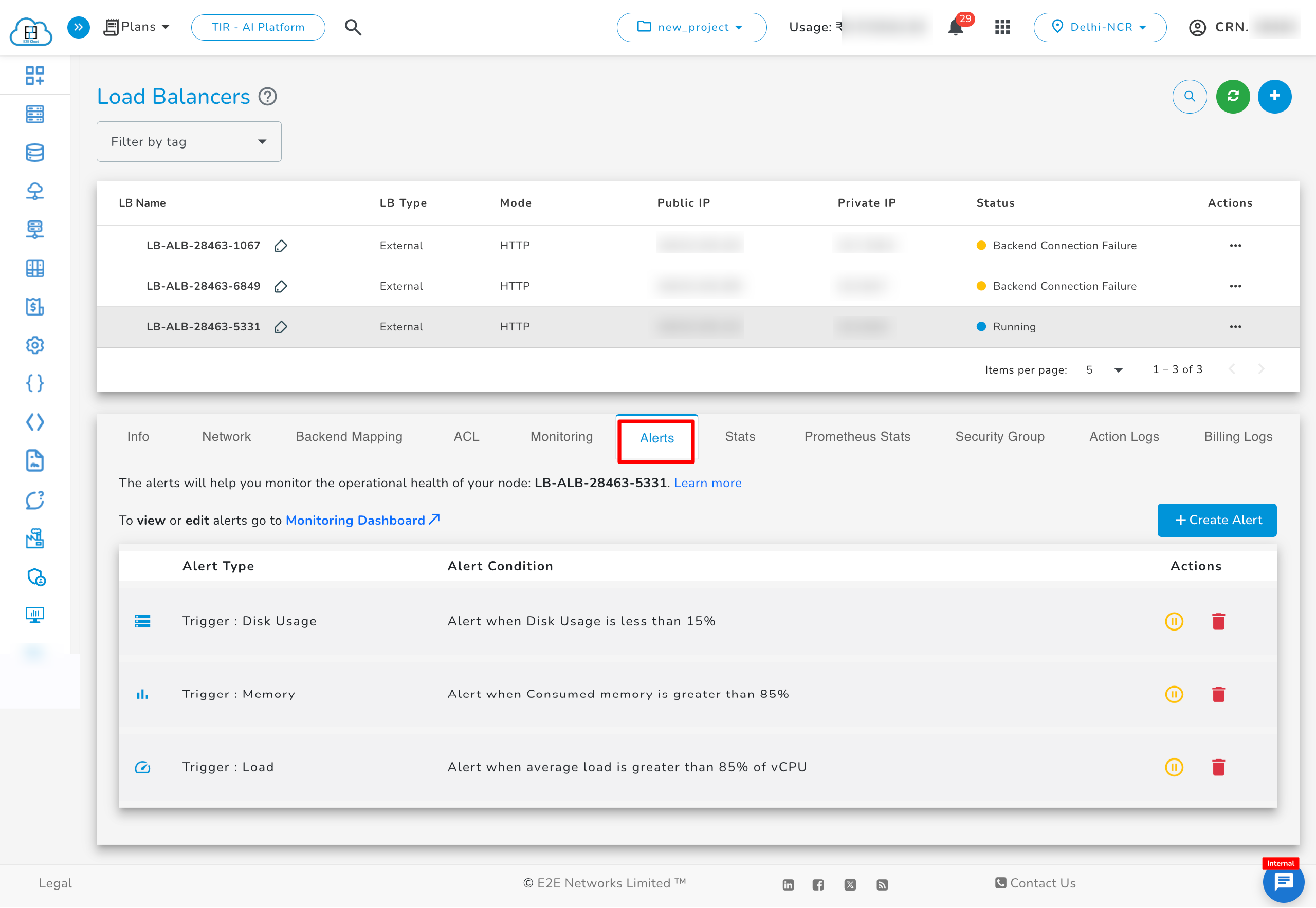
Alerts
Server health alerts are automatically created for your newly created load balancer using recommended parameters for alert policy. You can also set up new alerts by defining trigger parameters as per your use case. The alerting system works by sending automatic response notifications to your defined email list. Learn more.
Stats
The Stats tab provides real-time operational metrics for the load balancer, including frontend and backend traffic statistics. It displays session rates, active and maximum sessions, data throughput, request/response counts, error rates, and server health status. These metrics help monitor performance, identify issues, and verify the current state of all backend servers. The information is refreshed periodically to ensure up-to-date visibility into load balancer activity.
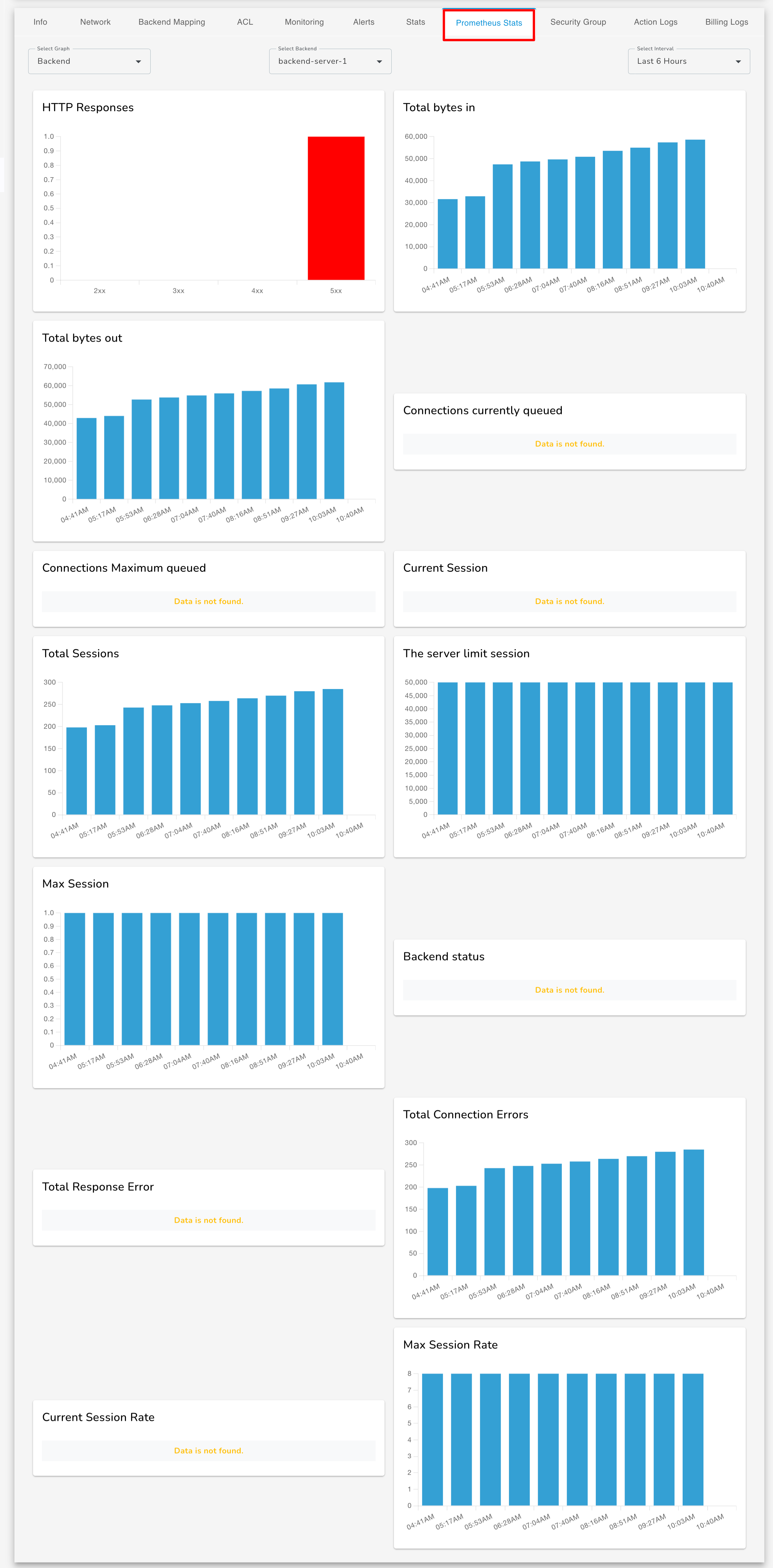
Prometheus Stats
Security group
When creating a Load Balancer, a default Security Group is automatically attached which can be shown below. You can also attach allow all traffic security group and a new security group.
Attaching a Security Group to the Load Balancer
- Click on Attach Security Group.
- From the dropdown list, select the desired Security Group. You can also select multiple Security Groups simultaneously.
- Click on the ✓ (tick) icon to confirm.
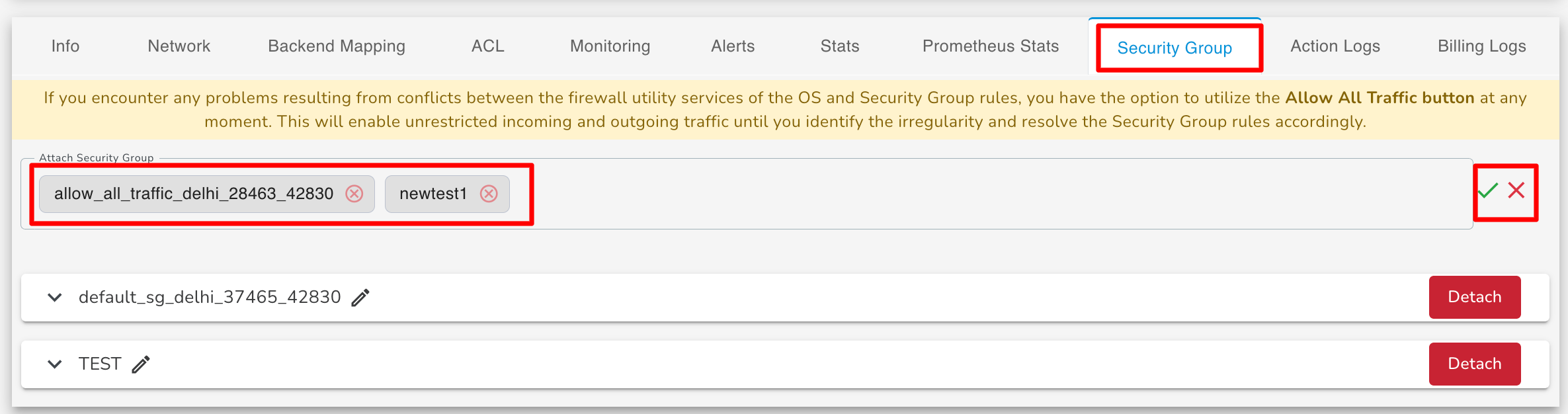
Note: You can attach multiple security groups at the same time. Once the operation is completed, a confirmation message will appear stating “Security Group attached successfully.”
- You can also manage the attached Security Groups later. The Load Balancer allows you to edit the currently assigned Security Groups or detach any Security Group that is no longer required. This gives you full flexibility and control over access management for your Load Balancer.
Action Logs
Action logs contain detailed information about requests sent to your load balancer such as the date/time the request was received, client’s IP address, request protocol, request paths, and server responses. These access logs are useful to understand incoming network traffic patterns and troubleshoot issues if any arise.
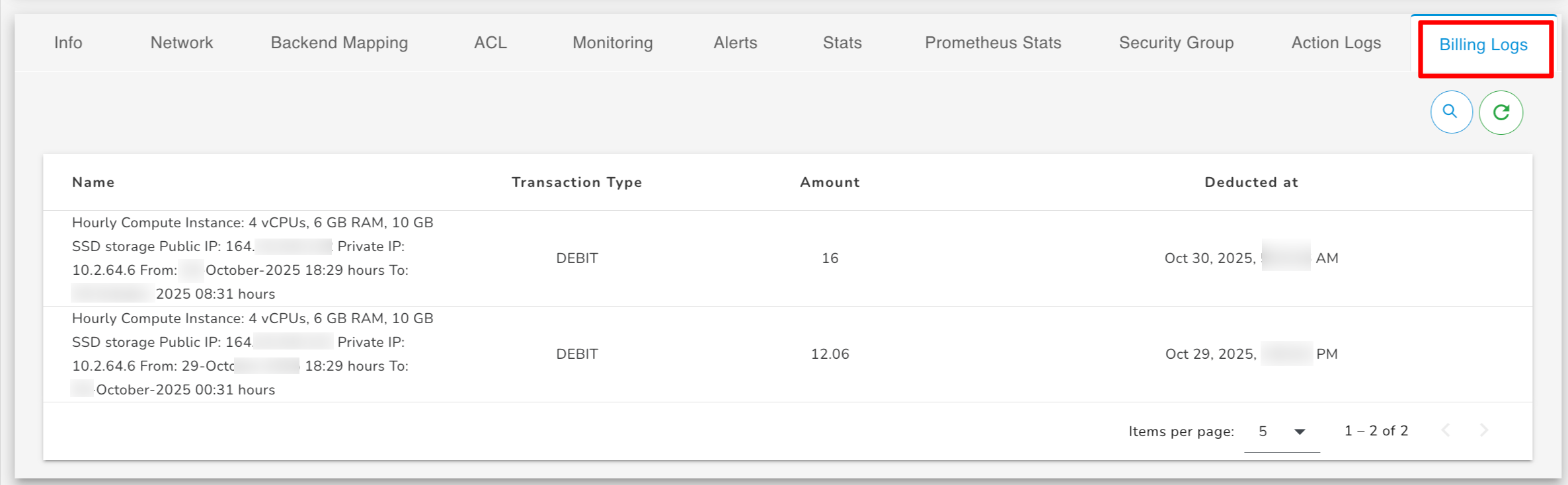
Billing Logs
Activity Timeline
The Activity Timeline provides a detailed, time-ordered history of all actions performed on your Load Balancer. It helps you track configuration changes, operational events.
Actions
Types of actions you can perform with Load Balancer.
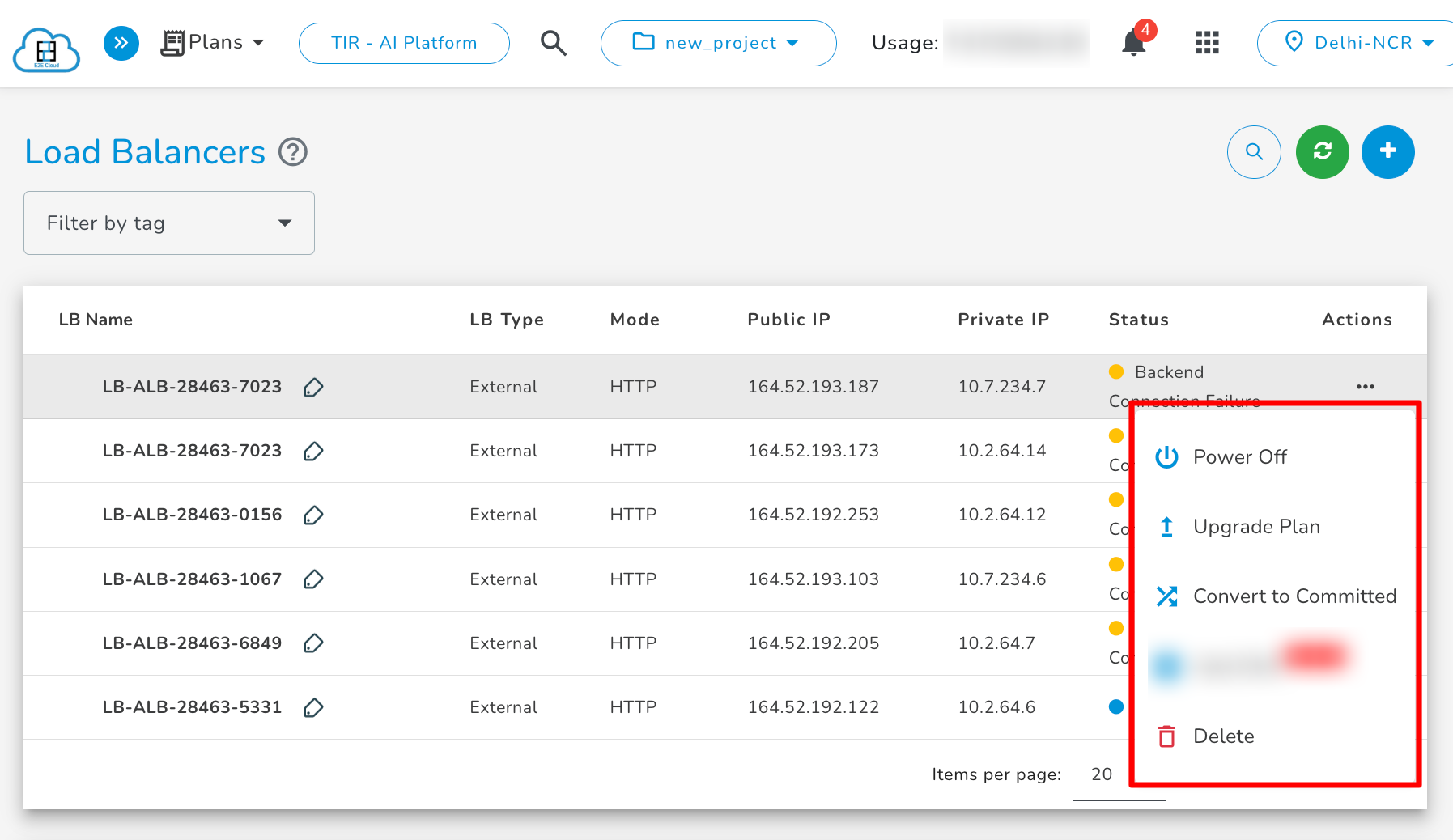
Stopping your Load Balancer
To stop your Load Balancer, click on the Stop button. A confirmation popup will open; click on the Power Off button to confirm.
Upgrade your Load Balancer
The LB upgrade feature enables customers to easily upgrade their LB plan based on their specific usage requirements. To upgrade your Load Balancer, click on the Upgrade button under the Action button.
After that, click on the Apply button with the selected plan. The upgrading process will then start.
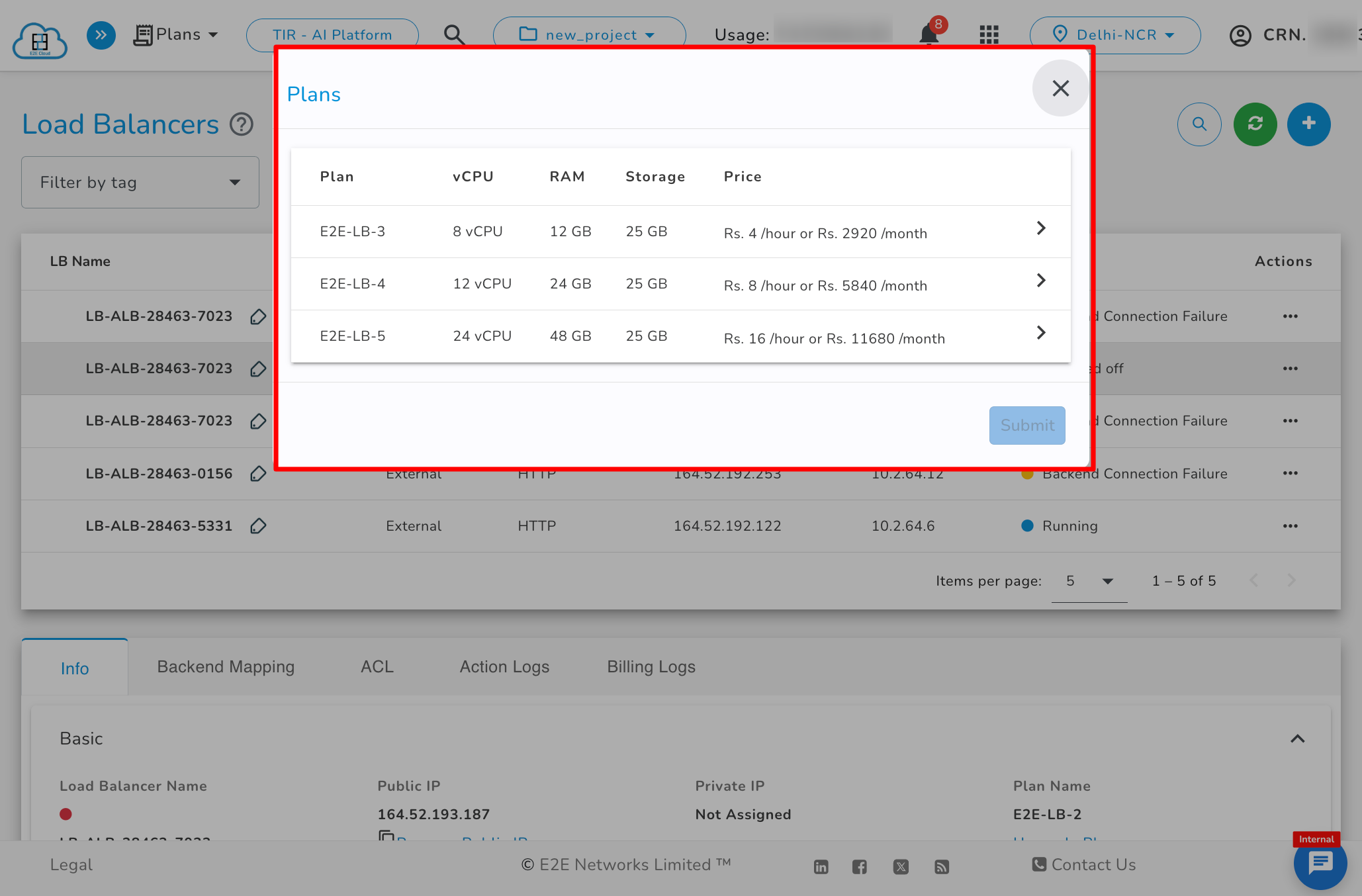
Note: Please ensure that your load balancer is stopped when performing the upgrade action.
Delete
To delete your Load Balancer, click on the Delete button.